Let’s be honest, who didn’t want to be James Bond when they were younger? There’s nothing cooler than having a secret mission and in the end, save the world.
Playing around with cryptography at a very basic level isn’t only fun for kids, it’s also a good learning opportunity. It’s a playful way to show them how it works, but also an opportunity to teach them that security and privacy are a good thing. Especially in the digital age we live in now, keeping some things a secret is of vital importance.
So let’s look at a couple of fun exercises (or experiments) you can do with your kids during the upcoming holidays.
Pigpen Cipher
One of the easier ciphers to understand is the pigpen cipher. There are different ways to draw the cipher (some don’t use a diamond shape, but use a cross for letters S to Z), but the working is the same.
Usage of this form of encryption is very old. There is evidence to suggest that the Knights Templar used a code like this during the Christian Crusades (1095–1291).
Let’s look at the pigpen cipher:

So how does it work? For each letter in the message you want to encrypt, you look for the position in the pigpen cipher diagram. You draw the shape of the box where you find the letter. When it’s the first letter in the shape, you just draw the shape, but if it’s the second letter in the shape, you add a dot in the center. An example:

Another alternative looks like this, where the diamond is drawn slightly different:

Caesar cipher
The Caesar cipher is named after Julius Caesar, who used it with a shift of three (where “A” becoming a “D” when encrypting, and a “D” becoming an “A” when decrypting) to protect messages of military significance. Caesar’s was the first recorded use of this cipher (around the year 56).
So how does it work? The sender and recipient agree on a number of rotations (in this case, let’s pick the original 3). That means that a D becomes an A, E = B, F = C, etc:

So with this, the text “Secret Message” becomes “Vhfuhw Phvvdjh”.
What’s also cool is building your own Caesar Wheel (or using an online version). That makes encrypting and decrypting messages a lot faster. You can create your own, or you can print out the example below, cut out the circles, and pin them in the middle with a peg for example:
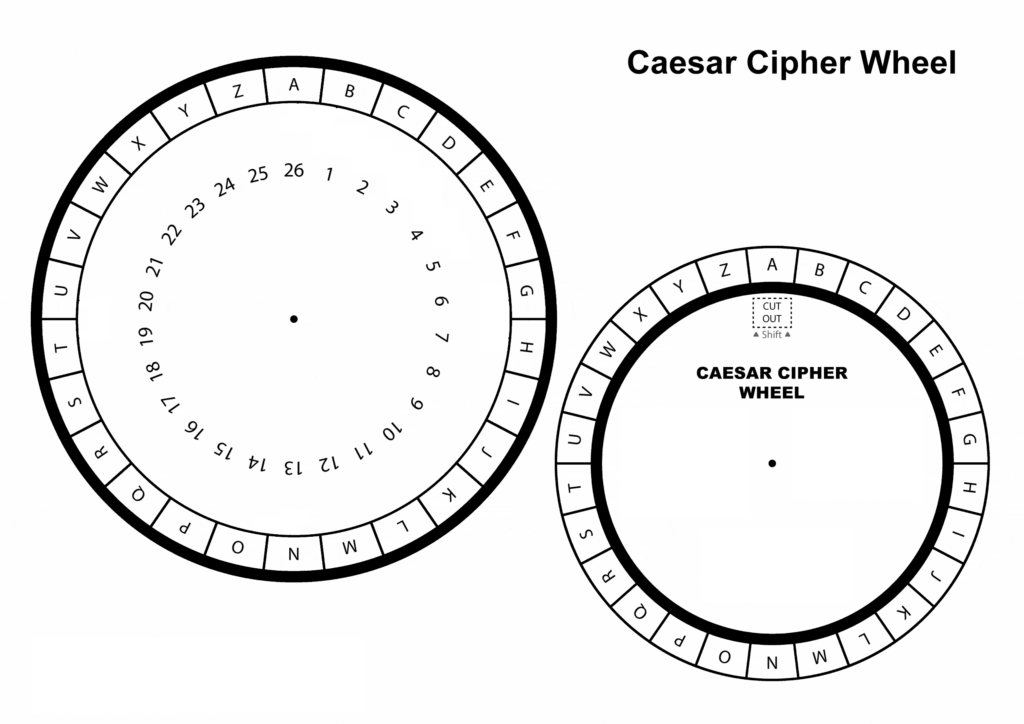
The outer ring will be used to find letters used in your plain text message, and the inner ring will show you the letter you need to use in your coded message.
Letter number code
The simpler variation of the Caesar cipher is to just replace letters with numbers. So A=1, B=2, C=3, etc.
With this system, “Secret message” becomes “19; 5; 3; 18; 5; 20; 0; 13; 5; 19; 19; 1; 7; 5” (the 0 represents a space).
Atbash cipher
The atbash cipher is a substitution cipher, where each letter is replaced by its opposite. You need to map the alphabet to it’s reverse, so A=Z, B=Y, C=X, etc:
In the table below, line 1 contains the plaintext characters, and line 2 the encrypted characters.
| 1 | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2 | Z | Y | X | W | V | U | T | S | R | Q | P | O | N | M | L | K | J | I | H | G | F | E | D | C | B | A |
The text “Secret message” will be transformed to “HVXJVG NVHHZTV”
Morse code
Around 1837 the morse code was invented, and in 1844 it was first used to send the first telegraphic message in he USA. It was still in use until 1999, when the last official ship-to-shore message was sent. Morse code doesn’t encrypt the data, it’s a way to encode your message. Using only Morse code, it doesn’t make your message unreadable if “intercepted”.
The Morse code alphabet looks like this:

You can either use this as an example, or use an online Morse code translator (this also allows you to listen to the audio version of a Morse code message).
The text “Secret message” in Morse becomes: “… . -.-. .-. . – | — . … … .- –. .” (the pipe symbol acts as a space between word in this example).
Tap code / Knock code
The tap code or knock code is an easy system to understand. It was created in 1965 by 4 American Prisoners of War (POW) to communicate with each other while in captivity in Vietnam. It allows you to encode messages letter by letter, and can be transmitted by tapping or knocking on something (for example a wall or table).
This code is based on a 5×5 grid:
| 1 | 2 | 3 | 4 | 5 | |
| 1 | A | B | C ( / K) | D | E |
| 2 | F | G | H | I | J |
| 3 | l | M | N | O | P |
| 4 | Q | R | S | T | U |
| 5 | V | W | X | Y | Z |
To code your message, you look for your letter in the grid, and use the number of the row, followed by the number of the column. For an A you would tap once, followed by another single tap. For an E, you would tap once, followed by 5 taps.
The message “Secret Message” becomes “4,3; 1,5; 1,3; 4,2; 1,5; 4,4; 3,2; 1,5; 4,3; 4,3; 1,1; 2,2; 1,5”.
Navajo code
The last one I want to add is a difficult one to use. The US Army used code talkers in World War 2, and it reminds most people of the stories about the Navajo code talkers in the pacific. But other Native American code talkers were also deployed to the North African and European theaters of war. After the war, the Japanese admitted that the Navajo code was the only code they were never able to break.
That shows you how difficult it is to use, because the code talkers used words from their native language(s) (only spoken by Native Americans) to reference letters in the English alphabet. Next to that, they could use different words to describe the same letter, for example the D could be Deer (Be), but it could also be Dog (Lha-cha-eh):

Also, they could use words to describe something, as well as spell it out. If they wanted to use the name France in a message, it could either be translated directly to “DA-GHA-HI” but FRANCE can also be devided into letters: MA-E (F), GAH (R), WOL-LA-CHEE (A) , NESH-CHEE (N), MOASI (C), DZEH (E).
Next to that they also had specific words to describe things:
| Word | Navajo | Literal translation in English |
|---|---|---|
| Dive bomber | GINI | Chicken Hawk |
| Battleship | LO-TSO | Whale |
| Squad (of soldiers) | DEBEH-LI-ZINI | Black sheep |
| Germany | BESH-BE-CHA-HE | Iron Hat |
| Tank | CHAY-DA-GAHI | Tortoise |
Scytale
Another practical code you could try is a transposition cipher , where the message is written on a piece of paper wrapped around a stick (called Scytale).
The paper is wrapped around the stick, and the message is written in a straight line. Now unwrap the paper, and fill the rest of the paper with random letters. The only way to decrypt the message, is to wrap the piece of paper around a similar stick as recipient. By doing that the message becomes readable again.
Transposition cipher
This cipher is harder to understand, but an explanation of this way to encrypt a message can be found here: Cryptography: Understanding the SOE code used in WW2.
Conclusion
Teaching your kids that it’s important to keep some things a secret, and not to share certain things publicly on social media, is an underestimated life lesson. Nowadays kids and adults don’t think twice about posting something online, not realizing it will be very difficult (or nearly impossible) to undo that.
Privacy is important for all of us. It’s not that you have anything to hide, but some things are best kept unshared.
Teaching your kids that life lesson might keep them safe in the future, or at least protect them from some online risks. And if you can introduce that concept in a playful manner through something as fun as encryption, spies and secrets, why not?
Disclaimer
This post is for informational purposes only, and we are not liable for any loss or damage resulting from its use.
Also: don’t be a skiddie, or an a-hole, and stay vigilant!
No responses yet